Get Compliant with TrueVault Polaris
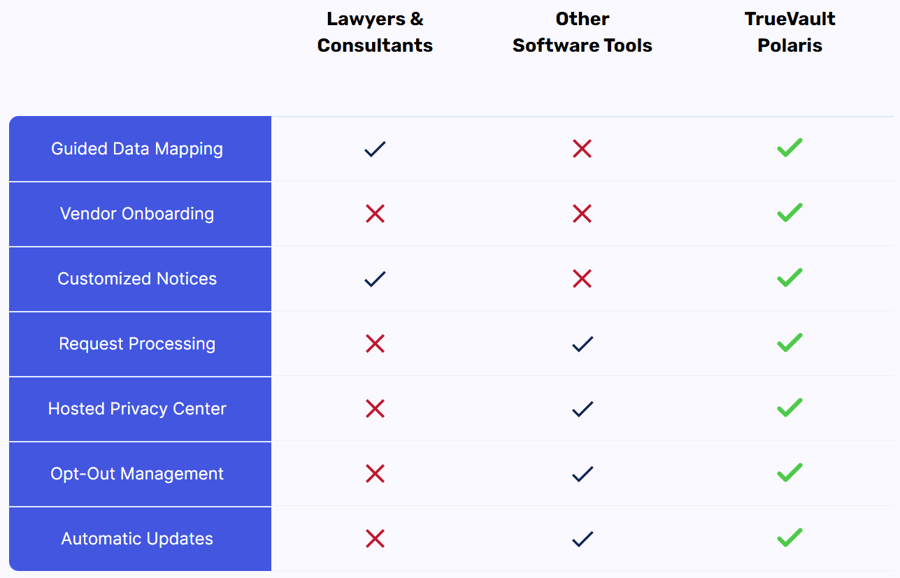
You don't have to be a privacy expert - or hire one - to get your business compliant with the CCPA, GDPR, and more.
TrueVault Polaris simplifies compliance through guided workflows and process automation, giving businesses of all sizes a full suite of privacy tools.
See the full list of privacy laws covered by TrueVault Polaris
Why Use Polaris?
Save Time, Save Money
Polaris helps you get compliant in days, not months, so you can get back to doing what you do best.
Privacy Expertise at Your Fingertips
You won’t be going it alone. We’ve integrated hundreds of hours of research into our easy-to-use tools.
No Pre-Existing Compliance Required
Other privacy solutions require you to already have a compliance program. Polaris helps you build one from the ground up.
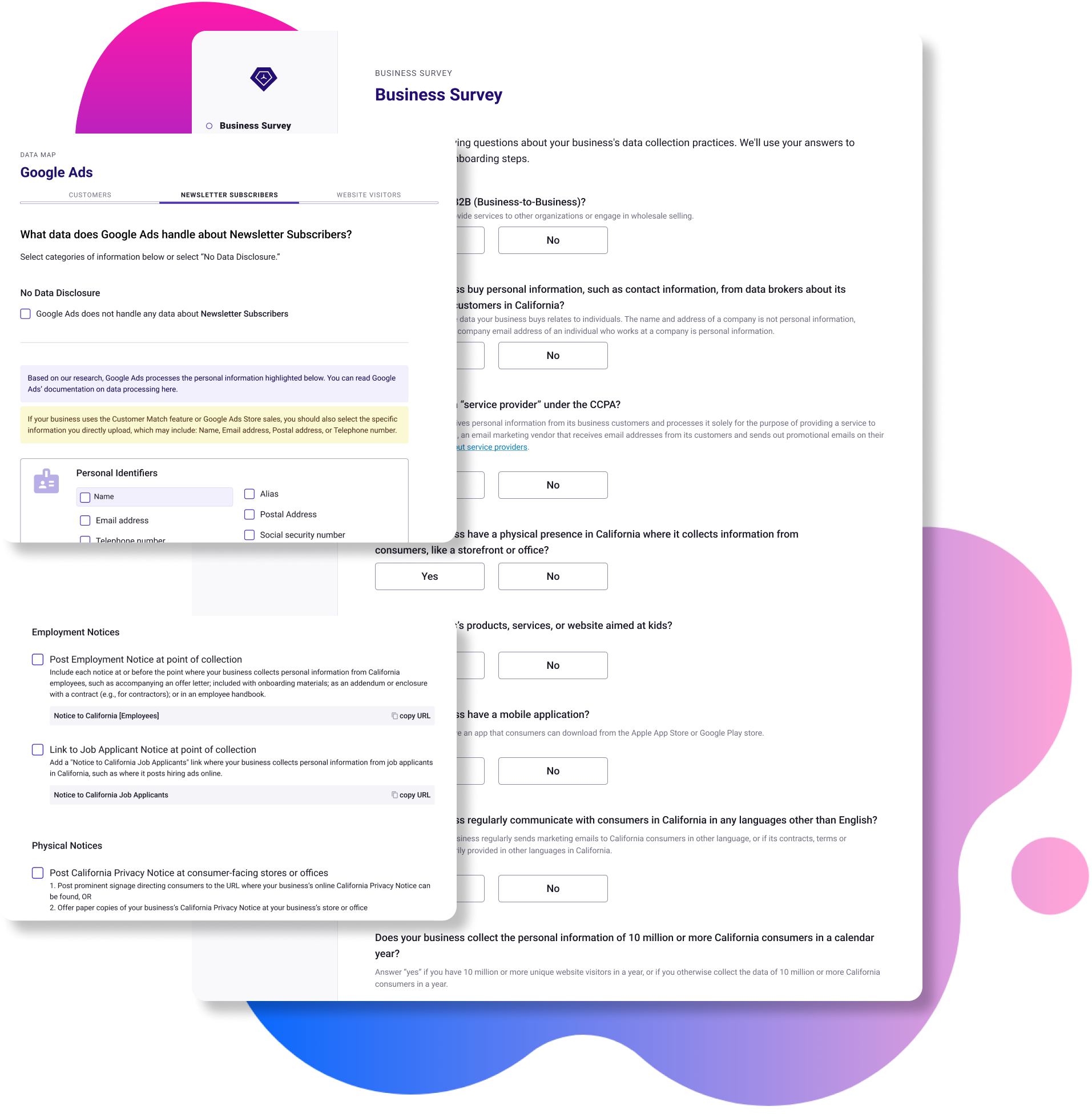
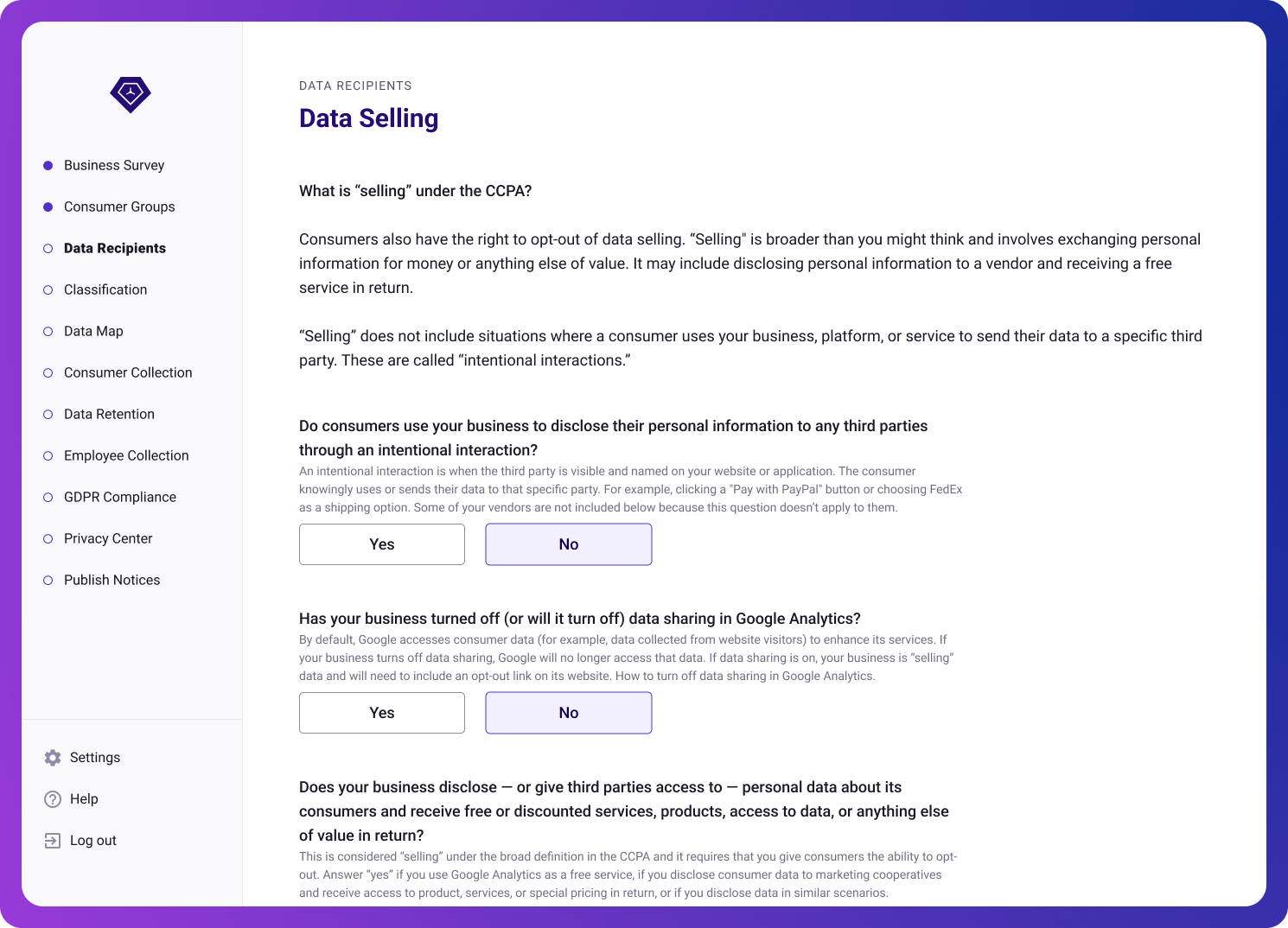
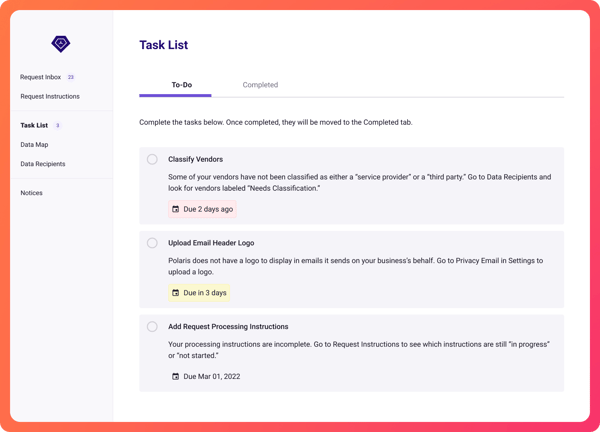
Step-by-Step Guidance
Our intuitive onboarding software makes it easy to get compliant. Just answer the guided questions, add any required information from your own records, and refer to our library of help articles as needed. If you can do your taxes online, you can Get Compliant with TrueVault Polaris.
Effortlessly Stay Up to Date
Consumer privacy laws are new and evolving. Polaris integrates the latest developments in privacy compliance so you can stay at the forefront of privacy without losing focus on your business.
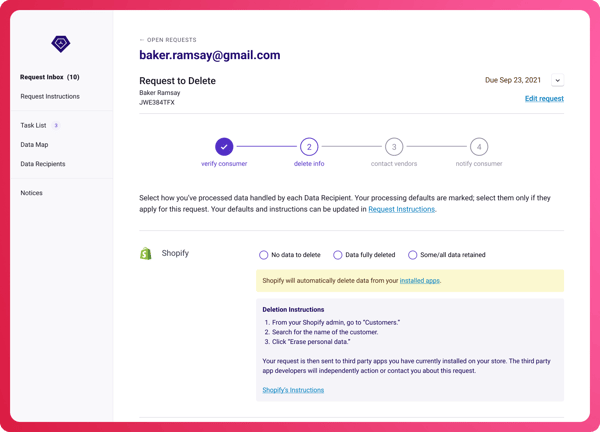
Privacy Requests Made Easy
Track consumer privacy requests from a single dashboard. Easily respond on time with our efficient, automated workflows.
Ready to Get Started with TrueVault Polaris?