What is PHI?
Last week, we broke down the working definitions of personally identifiable information (PII) as it applies to laws like GDPR and CCPA. But there are laws that extend even further beyond regulating how businesses can collect and store personally identifiable information (PII) when health information is involved.
Defining PHI
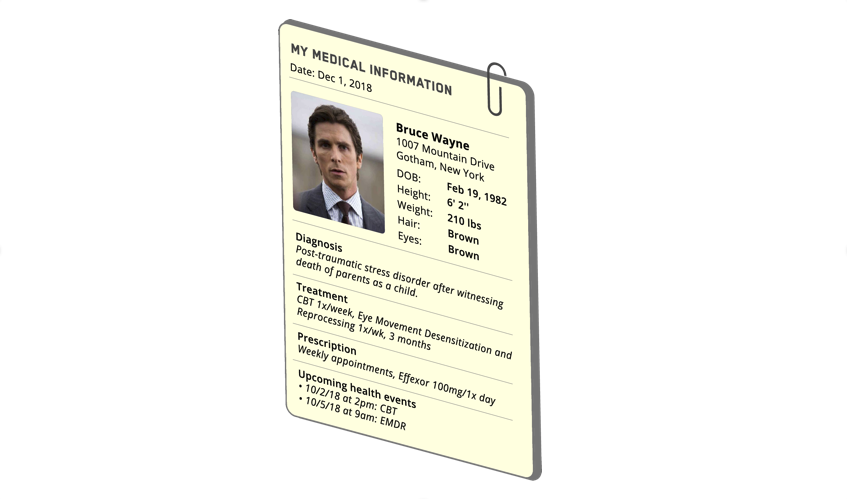
Protected Health Information (PHI) is the combination of an individual’s identifying information (e.g., name, address) and health information collected in the process of a medical appointment (e.g., medical record, conversations with providers, billing and insurance information etc.). 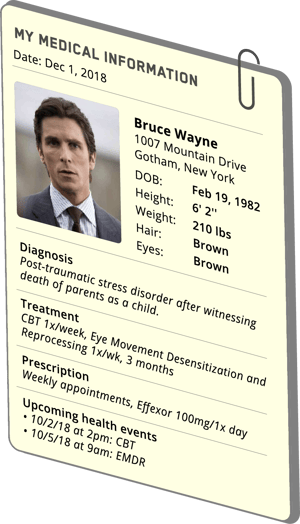
So, PHI = Personally Identifiable Information (PII) + health information.
Here’s an example of PHI: “Bruce Wayne is diagnosed with post-traumatic stress disorder”.
This information fits the definition of PHI because it contains PII (Bruce Wayne) and health information (post-traumatic-stress-disorder) and is therefore protected by Health Insurance Portability and Accountability Act (HIPAA).
Impacts of collecting PHI
Anytime PHI data is collected, a business must safeguard the data according to HIPAA, a federal mandate that outlines strict standards for protecting and storing PHI. These standards are extended to two parties: covered entities, any individual or business who provides treatment, payment or operations in healthcare; and business associates, any entity that uses or discloses PHI on behalf of a covered entity.
Here are some examples of potential Business Associates:
- Data processing firms or software companies that may be exposed to or use PHI
- Medical equipment service companies handling equipment that holds PHI
- Shredding and/or documentation storage companies
- Consultants hired to conduct audits, perform coding reviews, etc.
- Lawyers
- External auditors or accountants
- Professional translation services
- Answering services
- Accreditation agencies
- e-prescribing services
- Medical transcription services
In contrast, these folks are NOT Business Associates:
- Covered Entity's Workforce
- Individuals or companies with very limited and incidental exposure to health information, such as a telephone company, electrician, etc.
- Companies that act as a conduit for PHI, such as the postal service, UPS, private couriers, etc.
How PHI impacts your business
HIPAA was first written in 1996. Clearly the methods for data collection, import, and storage have advanced beyond paper medical forms and filing cabinets. The use of digital medical records and the transfer of data from a covered entity (e.g., a hospital) to a business associate (e.g., TrueVault) complicates how the law is applied.
One of the most common misunderstandings is that there is no “5-second rule” when it comes to PHI. HIPAA compliance is necessary whenever PHI is being used or stored. Yes, even if PHI simply “moves” through a server and is never stored on the server, it must be HIPAA compliant. Even if your application was not built with the intention of transferring or storing PHI, if it comes into contact with PHI at any stage, it must be HIPAA compliant.
When building a HIPAA compliant solution, you have two options: Option 1) Interpret how HIPAA applies to your company’s application and secure PHI in accordance with HIPAA. Option 2) Outsource the problem to a company like TrueVault or a hosting provider like AWS. If you do use a hosting provider, just make sure you consider the true costs.
Next week, we'll continue our blog series with a post on how de-identifying data can limit liability.
Download the HIPAA Compliant Checklist to learn the steps your business must take to securing PHI on the path to becoming HIPAA compliant.